Save 23% ($351) & Get a Free 1-1 Call with our Team ⏰ : 0d 2h 59m 43s
Don't get rugged! Staying Safe in Crypto
Using the technology is difficult for beginners. Scams, exploits, and other malicious attacks on the credibility of crypto by large players like FTX reinforce the idea that "crypto is a scam" and put people off participating, harming adoption.

Staying Safe in Crypto
Crypto often feels like one step forward, two steps back. Although there has been development in all areas of the market - there's still a huge issue with user experience.More recently, it has not been DeFi actors that have terrorized the crypto community. Centralized entities have wrecked confidence in crypto more than any DeFi exploit ever could. There has been a clear trend of centralized institutions grossly mismanaging customers' funds.
There are lots of things that we can do to protect ourselves from those who would see our funds rugged! In this journal, we’ll cover some simple tips to keep you and your crypto safe.
Disclaimer: This is not investment nor investment advice. Only you are responsible for any capital-related decisions you make and only you are accountable for the results.
Centralized Entities
One of the key factors that leads to users getting rugged by centralized custodians is trust. Users are led to believe that centralized parties are more trustworthy than decentralized actors. Hopefully, this year has proven that centralized actors are just as dirty as the worst actors in DeFi. Just take a look at the new FTX (bankruptcy) CEO’s filing on the state of FTX:
For perspective, John J Ray was the CEO that handled the Enron scandal. For him to say this is telling - he’s been to hell and back with some of these companies. Another factor is the lack of support for fiat payments to decentralized protocols/wallets. Getting your cash onto a platform to buy crypto is a pain point.
Unfortunately, centralised entities have a monopoly here. It’s the link between TradFi and DeFi that is the weakest because of the cross-over in regulation. Still, we believe CEXs etc should only be used when necessary. Everything that can be done on a CEX can be done on-chain nowadays (except for moving from a bank account to crypto).
But how do we stay safe whilst doing so?
Ledger – Cold Storage
Maintaining control of our assets as often as we can is the single most important rule we follow. As cliché as it is, we cannot stress enough the reality of “not your keys, not your coins”. This motto has been reinforced time and time again. However, the market has become complacent since events like the Mt. Gox nightmare and participants have been gravitating back to centralised custody. And look what happens as a result!Don’t give them the power to gamble away your money – keep control of your assets! You are the only one who can keep your funds safe. Take responsibility for your funds and learn how to protect them.
What’s the best way to do this? We recommend a Ledger!
Ledger is the industry leader in self-custodial products that help users stay safe. For more information on cold storage, click here. Additionally, have created a video tutorial to help readers set up and use a Ledger:
https://www.youtube.com/watch?v=gY7XlZ-zTB0
Seed phrase safety is also important – keep the written form as safe as possible. There are many ways of doing this. Would you still know your seed phrase if your home burned down? Flooded? Who has access to the location(s) of your seed phrase? Who knows about your crypto and how much you have? We’re not suggesting you start becoming suspicious of your family members or anything. However, these are all factors to consider. Just a bit of thought and common sense can go a long way!
We cannot stress enough the importance of self-custody – do not become a victim.
Hot Wallet Safety
After securing crypto in cold storage, there are other valuable tips we can give when using hot wallets. Using a hot wallet is often more convenient – for instance, if we trade a lot. However, it's important to note that only funds required for activities should be held online. Everything else should stay in cold storage. A good way to think about it is that assets in cold storage are in your bank, and assets in hot wallets are your spending cash.One of the key security measures that we can take when using hot wallets is to make sure our computer/laptop is protected. Free of viruses, free of keyloggers, and other malicious malware. Do regular virus scans and avoid any dodgy websites (crypto-related or not). Ensure that the device in use is as secure as possible - make sure there are no weak links!
Another security measure is distributing assets held in hot wallets across many accounts. This is especially important when dealing with several protocols daily. You never know which protocol might be compromised in the future, especially with how early in development a lot of these protocols are. If a compromised protocol has permission to access your wallet, funds in that wallet could be at risk. Having multiple accounts is a method of reducing any potential damage done.
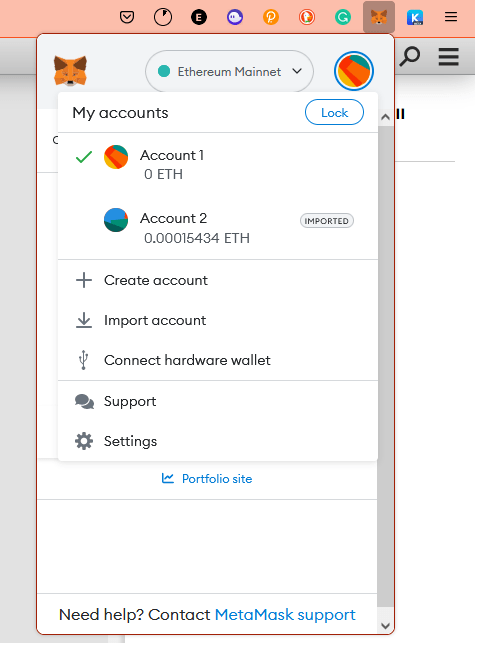
Sub-accounts can be recovered from the same seed phrase. But they have their own address and different public and private keys. This means that DApps can only get permission to access the selected account. You wouldn’t hand your bank card over to a shopkeeper and say “keep this until I come back”! You might keep your payment details saved, but financial crime is mostly insured in TradFi - not so much in DeFi.
Generally, it’s advisable to revoke access to DApps once you’ve finished using them. All wallets have this function – here’s an example for MetaMask:
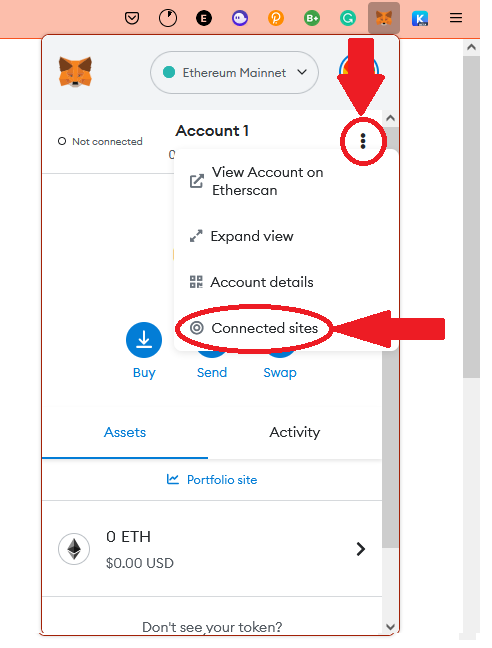
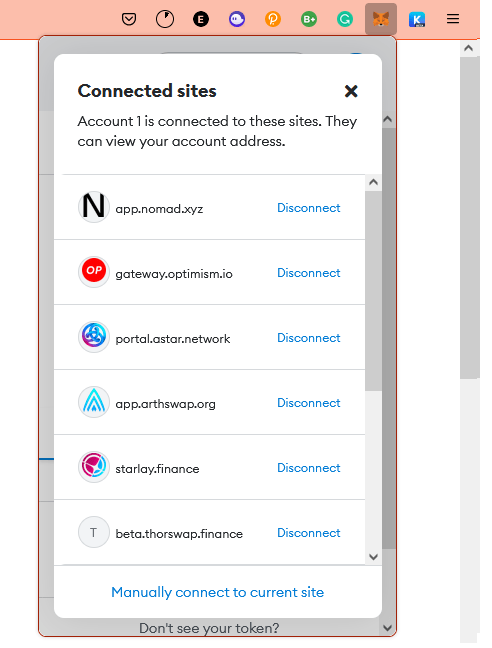
Disconnect from DApps – don’t take the risk! You can always reconnect whenever you need to use it again.
The last key point we’ll touch on is NFTs. It’s not uncommon for a seemingly random NFT to pop up in a wallet. If you did not purchase the NFT, or were not expecting one from an airdrop, then this is a huge red flag. Here’s an example:
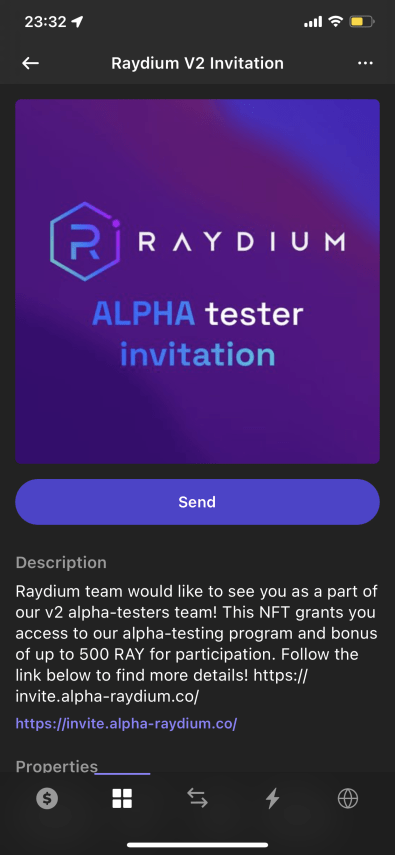
Raydium is a legitimate protocol on Solana. However, you will be drained if you click that link and connect your wallet. Simple as that - because this is not from Raydium. How do I know? Look at the web link - the real Raydium site is https://raydium.io/swap/. But the link in the NFT is close enough to get those who have heard of the protocol but haven’t used it in trouble.
Protocols will never send out anything like this, and any NFT that appears in your wallet that you haven’t applied for/asked for should be ignored. The NFT being in a wallet is harmless, but sending the NFT to a burn address is safer. For instance, use this address 0xb69Fba56B2E67E7DdA61c8aA057886A8d1468575 to burn Ethereum assets. All blockchains will have some form of address to send unwanted assets to. Get them out of your wallet. If you are still unsure whether the wallet is compromised, create a fresh wallet (storing the new seed) and transfer your assets over. Better safe than sorry.
To recap:
Keep your computer secure.
- Only keep the bare minimum required assets on hot wallets.
- Spread risk across many accounts.
- Always disconnect from DApps when not using them.
- Assume all unexpected NFT drops are dangerous.
DApp Safety Tips
Connecting to various DApps comes with its own issues. One safety procedure when connecting to a new DApp is ensuring the website is legitimate. There are fake websites everywhere trying to steal your assets. Connect to a malicious version and give permissions to your account - there’s a 100% probability your wallet will be drained.A simple method of ensuring we connect to the legit site is to do a quick search on CoinGecko:
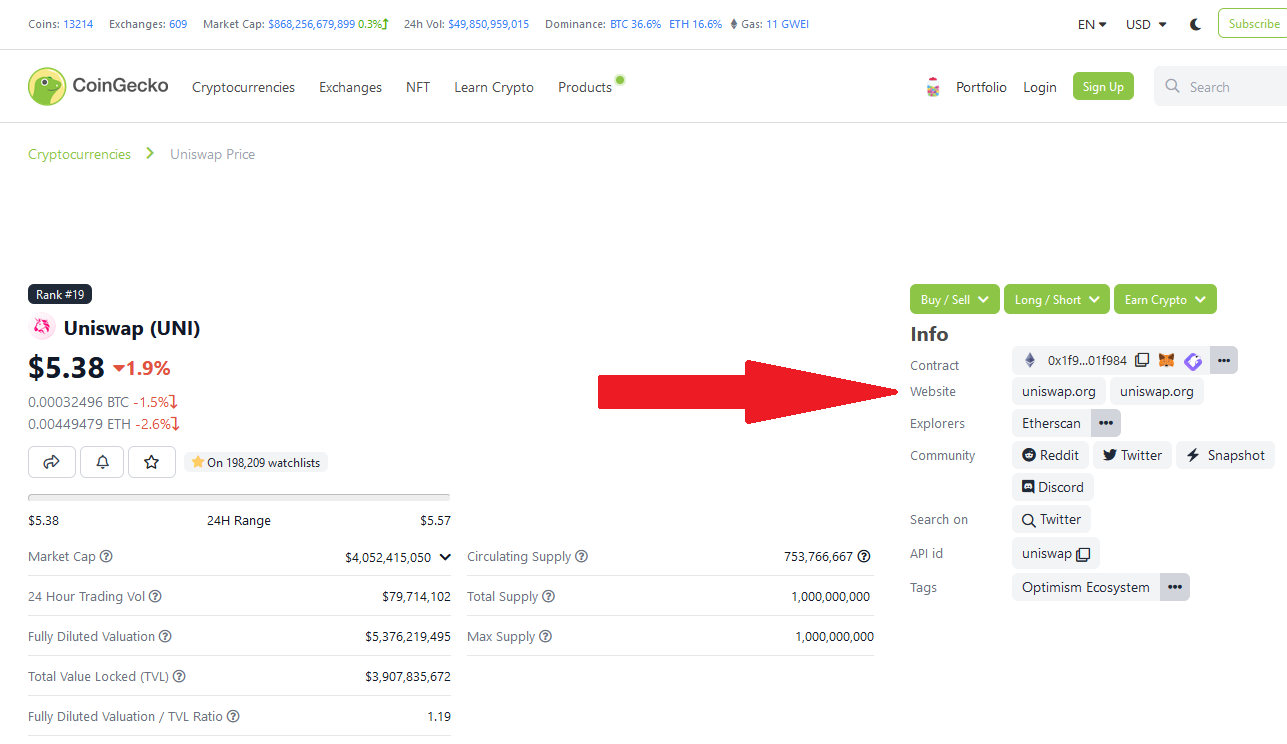
Go to CoinGecko, type the protocol you want to use, and go to their page – the correct link is readily available. Note that the links on CoinGecko will take you to the correct site. The protocol might still be a scam/rug/malicious. Always be confident that any DApp you use is not designed to be a rug/scam.
CoinGecko is also useful for checking the legitimacy of a smart contract. Whenever we connect to a DApp for the first time it's always beneficial to check the contract on the site lines up with the official contract:
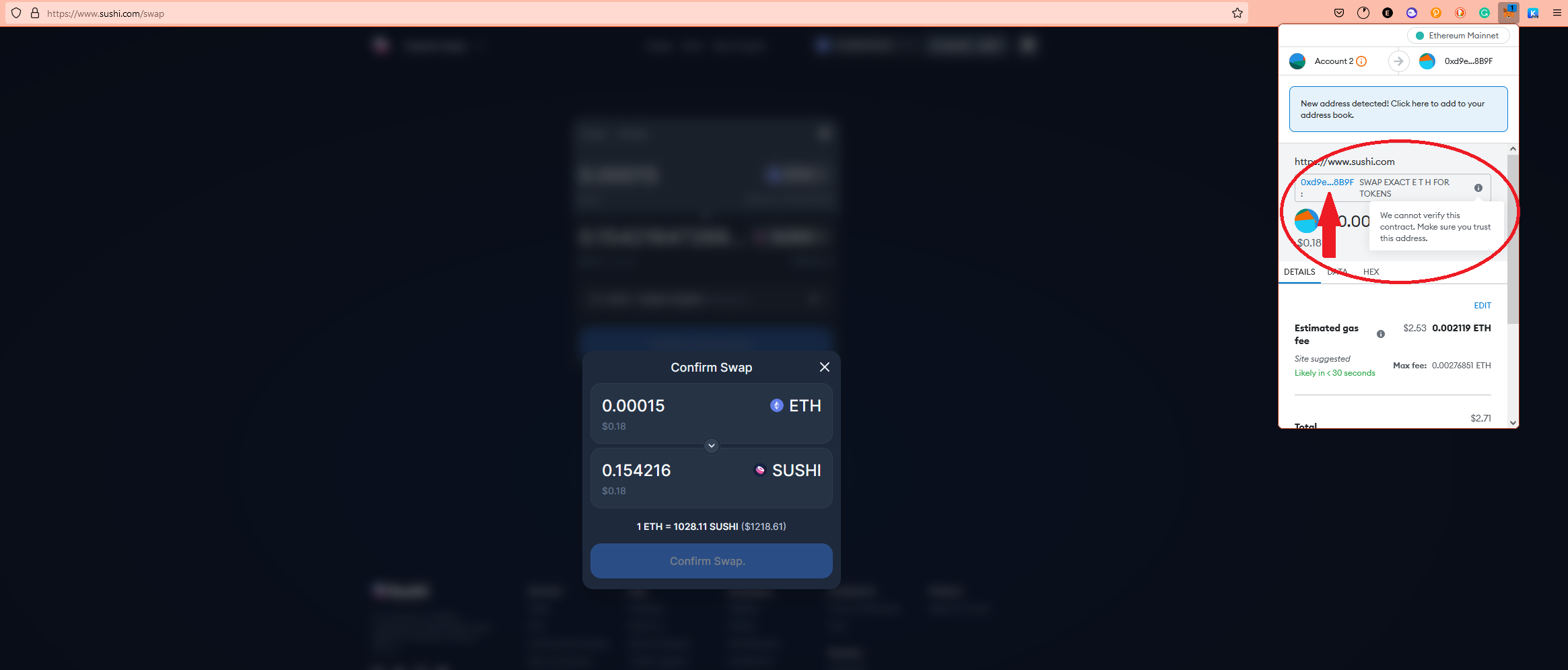
In this example, we’re interacting with SushiSwap to perform a swap. If we click the address (arrow), we can go to Etherscan to see the contract.
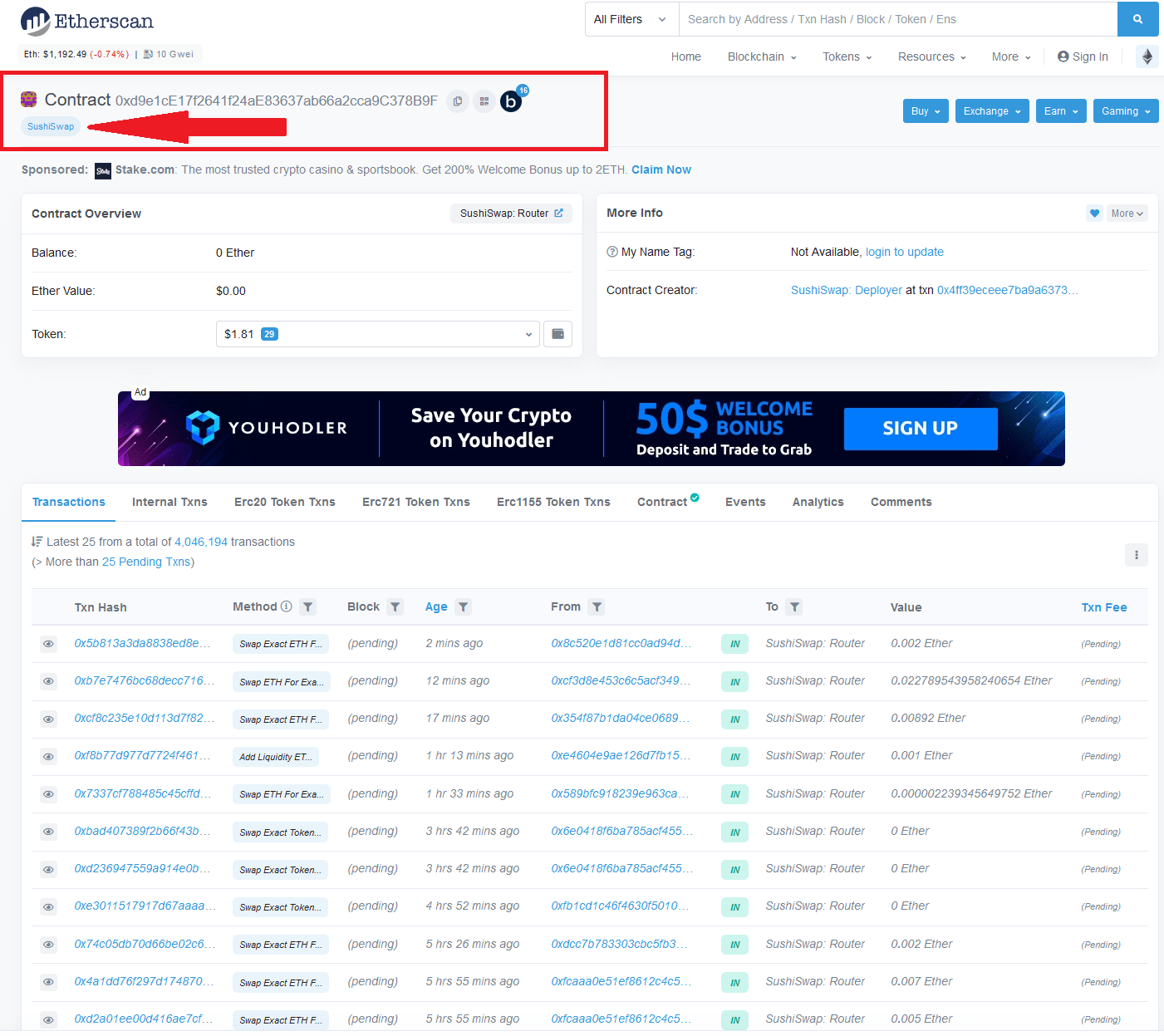
This simple check ensures we know exactly what our wallet is connecting to. Most chains have some form of scanner like Etherscan – use it! It’s free. The same method is applied to token contracts, NFT contracts, etc. For more information on on-chain analysis, click here.
The idea is to ensure we aren’t setting ourselves up for failure.
Wallet security can only go so far - a lot of losses could've been prevented by users doing a bit of due diligence!
Conclusions
Staying safe in crypto is more than just using a hardware wallet. Common sense is necessary too, and a little bit of time spent learning! We often get messages from members (and non-members) asking if there’s any chance of recovering funds. Unless the funds have been “misplaced”, there is little hope of recovering stolen or scammed assets.Do not let yourself become a victim. Using the blockchain may seem daunting at first but after a few transactions, it becomes easier! Pay attention to what you are doing – if unsure, do a test transaction. There’s no rush; make sure all addresses are correct and all DApps are legit.
If anyone has any questions or would like a second opinion, DM us. We’re here to help everyone, and we’ll always do our best to ensure you get the most out of crypto!




